T5-IDencode
Digital Identity Management
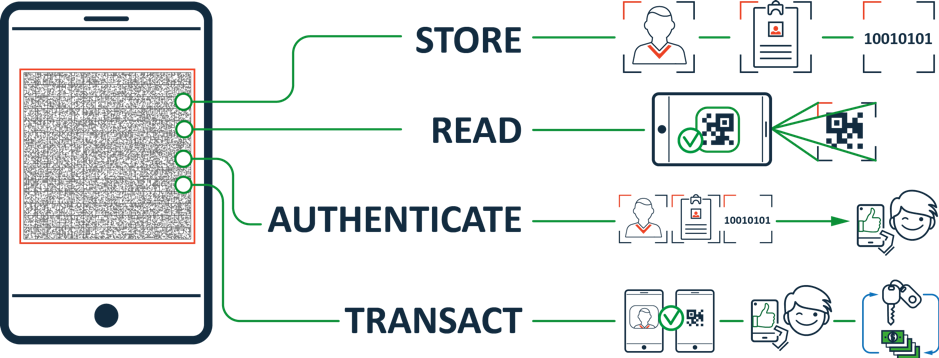
The T5-IDencode is a unique combination of advanced biometric and credentialing technologies enabling cost-effective Digital ID issuance and management.
The underlying T5-Cryptograph technology represents a digital container capable of packaging various forms of data for digital ID, such as demographic data, a highly compressed face image, as well as face and fingerprint biometric templates, all in an encrypted format. Data is protected by triple-level of encryption, including PKI.
The T5-IDencode is a completely offline solution for secure data packaging and multi-factor authentication.
T5-Cryptograph generated by the T5-IDencode enterprise platform can be read and decoded using a mobile device and a certified app. Despite its high-density nature for storing large amounts of data, the T5-Cryptograph reading process is fast and efficient.
Technologies

FACE IMAGE COMPRESSION ALGORITHM to compress face images to 1-kilobyte size

PKI and other technologies to encrypt the T5-Cryptograph
COMPLETELY OFFLINE SOLUTION for multi-factor customer authentication

LIVENESS DETECTION SOFTWARE to run liveness checks on face and fingerprint images
T5-FACE AND T5-FINGER TECHNOLOGIES to capture face and fingerprint images and convert it into biometric templates, as well as authenticate a person within seconds
T5-CRYPTOGRAPH TECHNOLOGY to package various forms of data for digital ID, such as demographic data, a highly compressed face image, as well as face and fingerprint biometric templates
Autonomous Self Authentication with T5-IDencode Technologies
Benefits for Business

PRIVACY & SECURITY
- PKI enabled non-repudiable secure code
- Hardware Security Module (HSM) generated encryption
- T5-Cryptograph is generated by the issuer at their location
- Verification of the T5-Cryptograph is completely offline and does not require access to the data issuer

COST EFFICIENCY
- Cost-effective alternative to smart cards (no chip needed)
- Can be issued in both Print & Digital formats
- Only a mobile device and a certified app are required to securely read and validate data
- Verification of the T5-Cryptograph is completely offline and does not require access to the data issuer
SCALABILITY
- Unifies issuer and verifier on a global scale within minutes
- Fully integrated biometric modalities like face and fingerprint
- The solution is designed to handle a very high volume of issuance operations
Benefits
for User
You decide who can access your ID
You decide whom to prove your ID
You authenticate in your own private environment



